Paper post orders and verbal briefings are where negligence cases get won against security contractors. Here's how to turn every handoff into a defensible audit trail.
The Handoff Is Where Liability Lives
Every security contractor has a version of the same scene. It is 2 a.m., the relief officer walks into the guard shack, the outgoing officer says "nothing new, same as last night," and a binder with three months of sticky notes sits on the desk. Nobody opens it. Six months later, a plaintiff's attorney opens it for them.
Guard shift handoffs are the weakest link in security operations. When officers rely on memory, improvisation, or whatever the last supervisor scrawled in a margin, instructions drift. The post order says one thing, the verbal briefing says another, and the actual behavior on site matches neither.
That gap is not a training problem. It is a documentation problem, and in a negligence claim it is the first thing pulled. Security guards who lack training will likely fail to respond well to any security incident, and when guards are unsupervised or do not have appropriate post orders, they are much less effective and often worse than having no security at all. That language is what plaintiff attorneys quote in opening statements.
The fix is not a better binder. It is not a thicker SOP. The fix is acknowledgment automation — a system that refuses to let a shift start until the officer has opened the current post order, confirmed understanding, and logged it against their identity, their post, and a specific document version. Everything downstream depends on that record.
Why Paper Post Orders Fail at 2 A.M.
Post orders are supposed to be living documents. In higher-risk locations, reasonable precautions may include trained security personnel, clear post orders, and documented monitoring practices, especially when the property advertises security or has a history of prior violence. On paper, every reputable contractor agrees with that standard. In practice, the binder on site reflects whatever the last quarterly review produced, minus the pages somebody borrowed and never returned.
The failure modes are predictable and they repeat across every contract:
- The inherited binder goes stale. The site was acquired from another contractor two years ago. Nobody has rewritten the post orders. The tenant list is wrong, the after-hours contact is retired, and the access code was changed last spring.
- Post-incident updates never reach relief. A trespasser tried to force a service door on second shift. The day supervisor wrote a new protocol. The overnight officer inherits the post the next evening and has no idea.
- Temporary special orders vanish into group texts. A client calls at 4 p.m. asking for a patrol sweep of the north lot at midnight. The account manager texts the guard on duty. The guard on duty is not the guard at midnight.
- Supervisors cannot prove who read what. Ask any ops director to produce, right now, a list of which officers have read version 4.2 of the post orders for a specific site. Most cannot.
The cadence collapses without a digital layer
Quarterly post-order reviews are the industry norm. That cadence works for the master document. It does not work for the reality of operations, where access hours change weekly, BOLOs land mid-shift, and tenant complaints trigger new patrol requirements in an afternoon. Paper cannot keep up, and neither can a shared drive nobody checks.
What "Acknowledgment" Actually Has to Prove
An acknowledgment is not a checkbox on a new-hire form. In the context of a claim, it is a discrete, timestamped record that ties four data points together:
- Officer identity. Who, specifically, read this. Not "the overnight team."
- Post and site. Where the acknowledgment applies. A gate post at Site A is not the lobby at Site B.
- Document version. Which revision of the post order was acknowledged. v4.1 and v4.2 may differ by a single sentence that matters.
- Timestamp. When the acknowledgment happened, down to the minute, ideally with GPS or geofence context.
That fourth layer — location context — is what converts an acknowledgment from a paper trail into a defensible one. An officer acknowledging a post order from the site's geofence at shift start is qualitatively different from an officer tapping "I agree" from their couch.
Important
If your acknowledgment system cannot answer "which version of which document did officer X read, where, and when" in under thirty seconds, you do not have an audit trail. You have a filing cabinet.
The bar is higher for armed or high-risk posts. For those, acknowledgment should include a short comprehension check — three to five questions that prove the officer actually absorbed the update, not just scrolled past it.
Gating the Clock-In: Making Briefings Non-Optional
This is the operational mechanic that changes behavior. An officer should not be able to clock in until the current post order is open, read, and confirmed. The logic is the same as credential enforcement: if the prerequisite is not satisfied, the shift does not start.
The sequence works like this:
- Officer opens the mobile app at shift start.
- App detects the assigned post and loads the current version of the post order.
- Officer reads, acknowledges, and — for high-risk posts — completes a brief comprehension check.
- Clock-in button unlocks. Time punch is stamped with the acknowledgment ID.
- If the officer tries to clock in without acknowledging, the system blocks the punch and flags the supervisor.
That last step is what separates a real gate from a suggestion. A pop-up that can be dismissed is not a gate. A time punch that cannot exist without an acknowledgment record is.
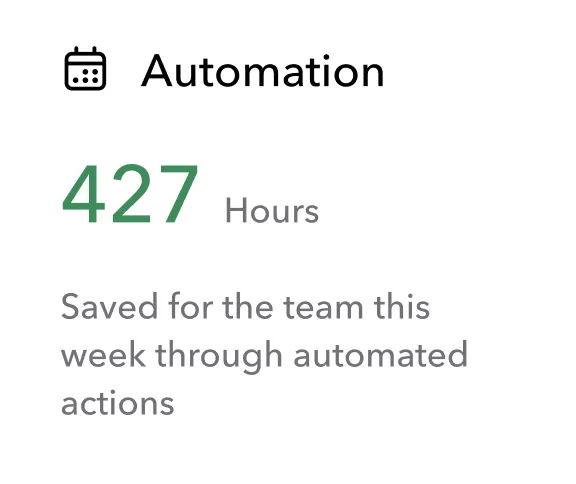
Teambridge builds this logic into the scheduling and mobile app surfaces that officers already use to pick up shifts and clock in. The acknowledgment flow is not a separate system bolted on — it is the same clock-in they run every shift, with the post order as a prerequisite rather than an afterthought. For contractors managing multi-site books of business, that consolidation matters because officers will route around any workflow that feels like a second app.

Pushing Updates Mid-Shift Without Losing the Audit Trail
Shift-change acknowledgment solves the scheduled case. It does not solve the 11 a.m. tenant call that changes access hours for the rest of the week, or the BOLO that has to reach every officer on duty in the next ten minutes.
Real operations require mid-shift distribution with the same audit rigor as shift start. That means three capabilities stacked together:
- Instant modification. The post order is edited in one place and every downstream copy updates immediately. No re-printing, no re-emailing, no pulling binders from the field.
- Targeted push. The update goes to every officer currently on the affected posts, and only those officers. The lobby team at Site C does not need a notice about the loading dock at Site A.
- Re-acknowledgment with SMS fallback. Officers re-acknowledge the new version. If the app is closed or the officer has not opened it within a set window, an SMS fires as a fallback so the message lands even when the native notification does not.
That last piece is where most systems fail. App-only notifications assume the officer has the app open. Officers on a patrol tour do not. SMS fallback through broadcast messaging closes the loop and, critically, logs the delivery and acknowledgment timestamps the same way the app does.
Why the audit trail has to survive the update
When version 4.2 supersedes 4.1 mid-shift, the record of who acknowledged 4.1 does not disappear. It has to persist, time-bounded, because an incident at 1:47 p.m. under version 4.1 is judged against 4.1, not against whatever version shipped at 3 p.m. Version history is not a nice-to-have. It is the spine of the audit trail.
Tying Acknowledgment to Credentials and Site Eligibility
Acknowledgment is necessary but not sufficient. An officer can read the post order perfectly and still be the wrong officer for the post. Armed posts require armed certification. Healthcare sites require additional training on HIPAA-adjacent protocols. Federal and GSA contracts carry specific experience minimums and clearance requirements.
Credential gating and acknowledgment gating have to stack. The clock-in logic evaluates both:
| Check | Blocks clock-in when... | Risk if missed |
|---|---|---|
| Post order acknowledgment | Officer has not opened current version | Negligence exposure on incident response |
| Armed certification | License expired or not on file | Criminal and civil liability, contract breach |
| Site-specific training | Officer not trained for this post | Contract breach, insurance denial |
| Background check recency | Check older than contract requirement | Negligent hiring claim |
| Scheduled eligibility | Officer not assigned to this post | Payroll and coverage disputes |
This matters because the case law on negligent hiring and training is well established. A security company may have thoroughly investigated its job applicants but failed to train them. Handing someone a uniform and a badge without making sure that he has the skills to handle foreseeable circumstances is negligent training. It can subject the security company to liability for damages. A system that lets an uncertified officer onto an armed post, or an untrained officer onto a healthcare site, is the system that produces those claims.
The admin tools layer is where operations teams see credential status, expirations, and training gaps across the book, and it is where the clock-in gate draws its pass-fail decision. See Teambridge for security staffing for how license tracking and post-order workflows are configured together.
What the Audit Trail Looks Like When a Claim Lands
Consider the realistic scenario. Incident at 3:14 a.m. on a Tuesday. Plaintiff files six months later. Discovery requests every document the contractor has relating to the officer, the post, the shift, and the protocols in effect. What does the contractor hand over?
The automated record
- 22:47 — Officer J. Rivera acknowledged post order v4.2 for Site 14, North Gate, from within site geofence.
- 22:49 — Supervisor briefing acknowledged, covering updated BOLO issued 14:30.
- 22:51 — Clock-in recorded at North Gate, GPS-verified.
- 23:30 — Patrol tour #1 completed, all checkpoints scanned.
- 00:45 — Patrol tour #2 completed.
- 02:15 — Patrol tour #3 completed.
- 03:14 — Incident detected at loading dock.
- 03:16 — Officer acknowledged incident protocol v2.1, dispatch notified.
- 03:22 — Incident report filed, geotagged.
That is a defensible record. Every step is timestamped, tied to a specific document version, and geofence-verified. A plaintiff's expert can argue interpretation. They cannot argue the officer did not know the protocol.
The binder-and-verbal record
- A binder, last formally reviewed seven months ago, with some handwritten updates.
- A time punch from a standalone system showing clock-in at 22:51.
- A paper incident report filed the next morning.
- No record of what the officer read, when, or which version.
To hold a property owner legally responsible, an attorney will generally need to prove duty, breach, and causation — that the property owner had a legal duty to provide a reasonably safe environment, that they failed in that responsibility by not providing adequate security measures, and that this failure is what led to the injury. The binder-and-verbal record makes the breach argument easy. The automated record makes it hard.
For more on how negligent security claims are structured, see this overview from Justia on inadequate security liability.
Warning
In a deposition, the question is not whether your post orders exist. It is whether the officer on duty had read the version that applied to them at the time of the incident. If you cannot prove the answer, the jury assumes the worst.
Moving Off the Binder: A 30-Day Implementation Path
The good news is that acknowledgment automation does not require a full platform replacement. Most contractors can pilot it in 30 days across two sites and scale from there.
Week 1: Digitize and version
Pull the existing post orders for every site in scope. Assign a version number to each (start at 1.0). Strip out the genuinely outdated material — the contact list for the property manager who left in 2019, the protocol for the tenant who vacated last year. Upload the clean versions into the system of record. Tag each document by site, post, and risk classification.
Week 2: Configure clock-in gating at pilot sites
Pick two sites — one standard, one high-risk — and turn on acknowledgment gating for clock-in. Configure geofence boundaries. For the high-risk site, add a three-question comprehension check. Confirm that the time punch cannot occur without the acknowledgment record.
Week 3: Train supervisors on updates and dashboards
This is the step contractors skip, and it is the one that determines whether the system sticks. Supervisors need to know how to push a mid-shift update, how to target it to affected posts, and how to read the acknowledgment dashboard. Show them the view where they can see, in real time, which officers on shift have and have not acknowledged the latest version.
Week 4: Expand and set the review cadence
Roll to the full book. Set the quarterly review cadence inside the system, with automatic reminders to account managers. Configure the renewal alerts for credentials so license expirations feed the same clock-in gate.
Tip
Run the pilot with supervisors who are skeptical, not supervisors who are enthusiastic. The skeptic will surface the edge cases that break the workflow. The enthusiast will tell you everything is fine until it is not.
The end state is simple. Every shift starts with a documented acknowledgment against a versioned post order, tied to a verified officer at a verified post. Every mid-shift change flows through the same system. Every incident report lands in a record that already contains the context a claim would demand.
That is not a document management upgrade. It is the difference between a defensible operation and a discoverable one. The contractors who get this right stop treating handoffs as the weakest link and start treating them as the strongest piece of evidence in the file.
See the full workflow in context on the Teambridge platform and the security staffing page.